In the ever-evolving landscape of cybersecurity, password cracking remains a crucial, if controversial, tool. It's a double-edged sword, employed by both the guardians protecting our digital vaults and the malicious actors seeking to breach them. Despite alternative authentication methods, passwords persist as the ubiquitous gatekeepers to our online identities. As such, assuring their strength and confidentiality defines their success.
Inevitably, password cracking is intrinsically tied to GPUs. But today's market is flooded with demand from cryptocurrency miners and AI researchers, making GPUs notoriously difficult and expensive to acquire.
Fortunately, we can leverage cloud providers and hyperscalers (like AWS) to unleash a virtual army of GPUs for your password cracking needs. Let's explore how to set up an AWS environment so you can create security infrastructure on-demand. (If you're on another provider, like GCP or Azure, you should be able to adjust these steps minimally to accomplish the same thing.)
Setting up an instance
Currently, AWS EC2 provides two classes of GPU machines you could rent: P series machines (running either A100 or V100 GPUs from NVIDIA) or G Series machines (providing a small array of different GPUs from NVIDIA or AMD.)
We can fire up a number of g4dn.12xlarge instances as needed for this kind of work. Each instance carries 4 NVIDIA T4s, 192 GB RAM, 48 vCPUs, and some SSD storage. This is plenty for your average job. (If you really need a little more power, the g4dn.metal instances carry 8 GPUs.)
Warning
If you have a larger budget, p3 or p4 instances are going to be faster, but they will need additional steps to configure properly. You must properly install the fabric manager for your driver (nvidia-fabricmanager-*) if you are using these instances. the g4dn does not need this.
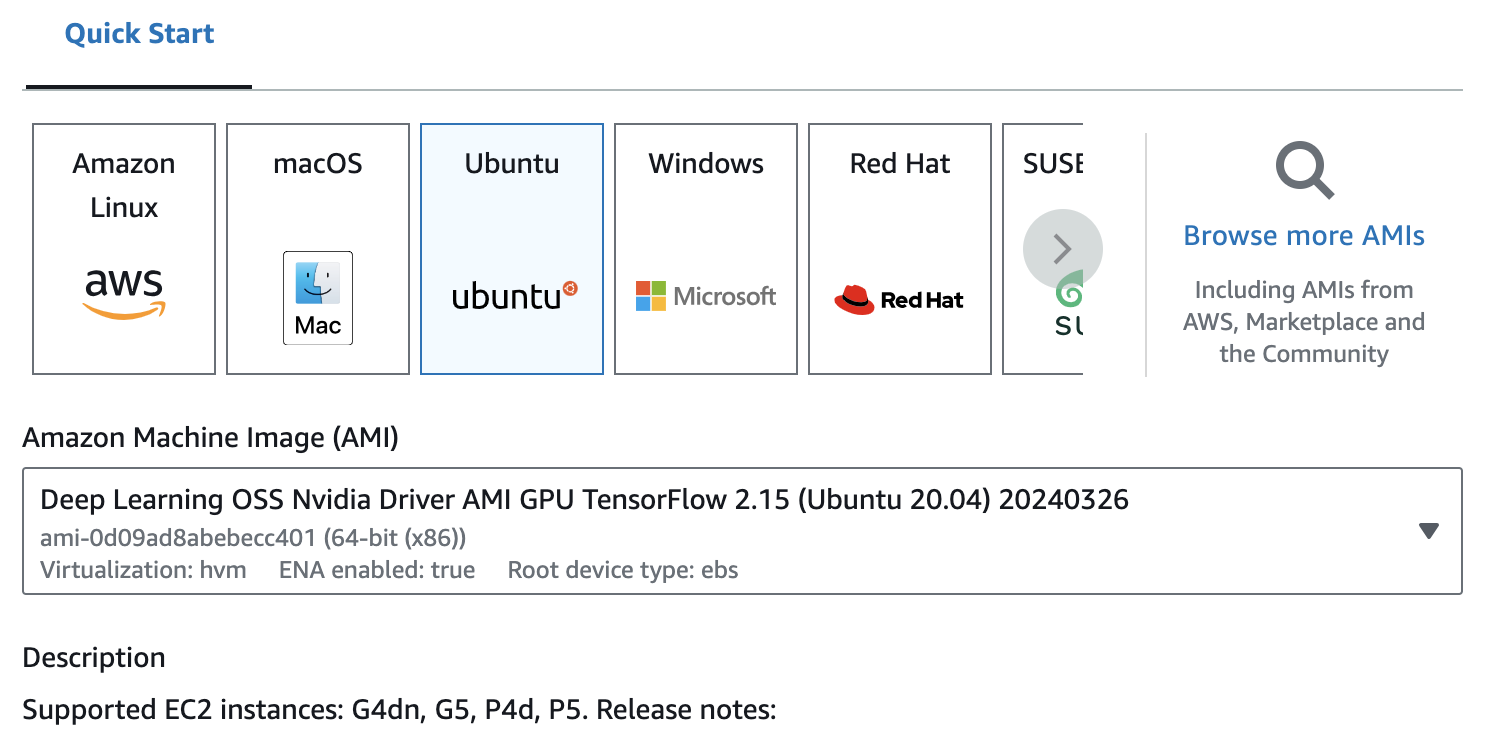
When choosing an operating system for your AWS instance, you have flexibility. However, Ubuntu is considered the canonical OS for Hashcat development, so we will stick to that. To save you some time and effort, we will leverage pre-configured Deep Learning GPU-based Amazon Machine Images (AMIs). These AMIs come pre-loaded with the necessary drivers and tools, eliminating the need for manual configuration like blacklisting the nouveau drivers. This shortcut allows you to jump right into password cracking rather than fighting with your system. 🙂
Log in to your EC2 console and navigate to the Launch instance button.
In the Application and OS Images section, go to the "Quick Start" selections and choose "Ubuntu". Below this, you should now be able to select a deep learning image with TensorFlow. (We generally select images with TensorFlow because their configs are historically the most stable with Hashcat.)
Ensure the instance type is set to g4dn.12xlarge.
Create a new key pair for this system.
In Network settings, use the drop down in Allow SSH traffic from to be "My IP" (and validate that it has your correct IP.)
When you are ready, select Launch instance on the right.
Once the system boots, log in via ssh. We still want to configure some additional packages for our environment, and install both hashcat and the util PACK. You can run the following commands individually, or place them in a script to run:
export DEBIAN_FRONTEND=noninteractive
## prep the box
sudo apt update
sudo apt install -y build-essential
## install perl deps
sudo apt-get install -y libconfig-tiny-perl libwww-perl libxml-simple-perl libnet-sslglue-perl
## install opencl installable client driver (ICD)
sudo apt install -y ocl-icd-opencl-dev
## deps for PACK
sudo apt install -y python3-enchant
## utils for general work
sudo apt install -y p7zip
## setup hashcat
git clone https://github.com/hashcat/hashcat.git
cd hashcat
make
## setup pack
cd ~
git clone https://github.com/Hydraze/pack
Now let's test our setup and confirm everything is working.
$ cd ~/hashcat
$ ./hashcat -b | tee benchmark.txt
You should get some benchmarking output (this output will also save to a file named benchmark.txt). That's it!
By leveraging the power of AWS and Hashcat, you've unlocked a powerful and scalable solution for password cracking. This approach eliminates the need for expensive, hard-to-find GPUs, allowing you to crack hashes with significantly faster processing speeds.
Remember, password cracking is just one piece of the cybersecurity puzzle. Always adhere to ethical hacking practices and obtain proper authorization before conducting any testing.
